aNewDomain.net — These examples, so precise they may have actually happened to you, are social engineering tricks of the trade brought to you by Lamont Wood. For your security’s sake, read on.
The digital landscape is flooded with innumerable viruses. From Trojans and zombie-botnets to worms and hijackers, the stealthy tech world poses one legitimate question: How can you best protect your system?
Image credit: Wikimedia Commons
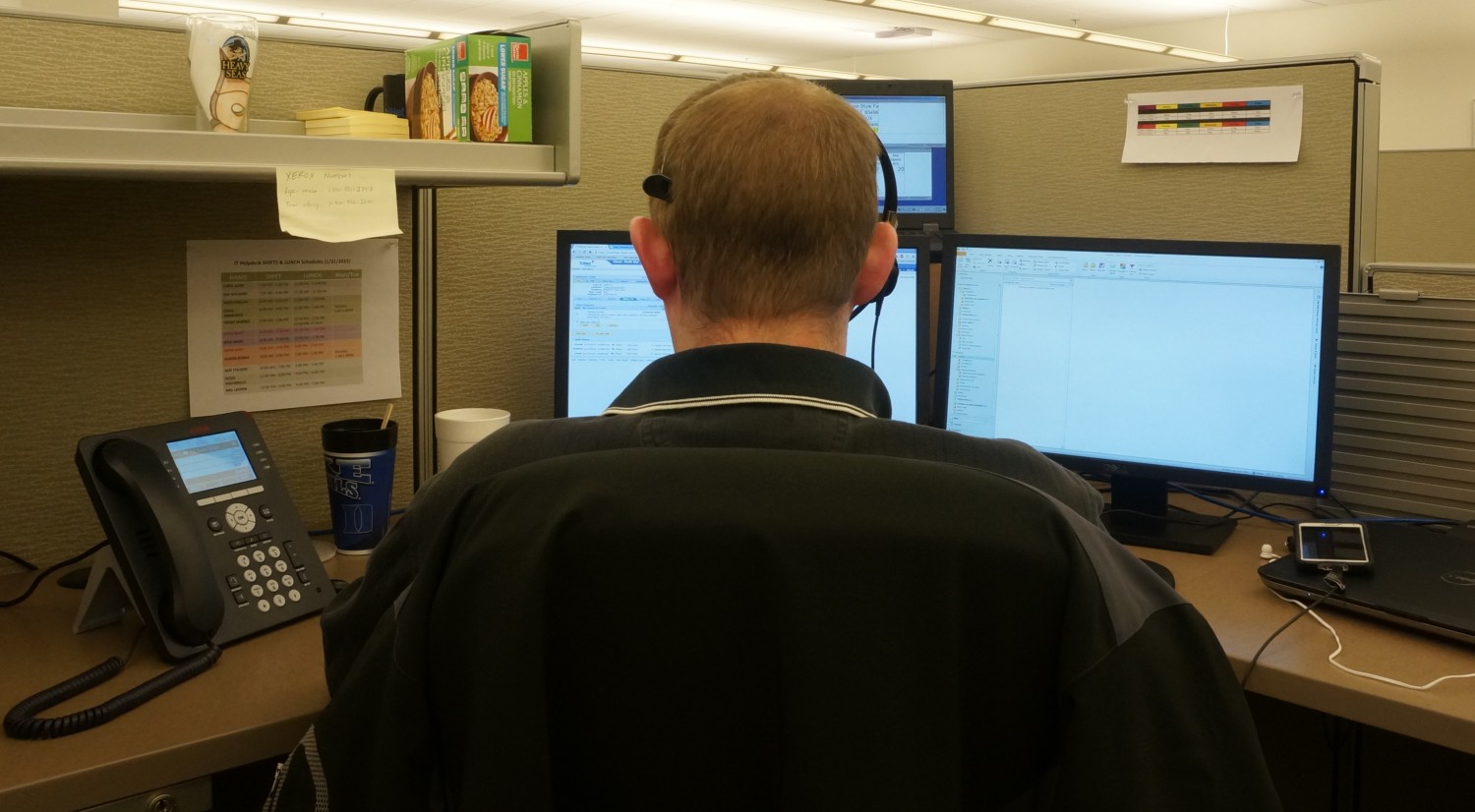
A firewall is the simple, straightforward answer. This wall of digital flame keeps pests from the Internet at bay. Antivirus software is a step up and ensures your computer is free of the dreaded bot master … <a half a minute passes> Pardon that brief break. Some kid claims to be our new intern. He’s working with Smith, apparently, which is strange because Smith is in Paris at a conference. Everyone knows that. I left the kid in a cubicle with his laptop while we get this sorted out.
To continue, security technology is of the utmost importance. A solid step is to encrypt your files with a 256-bit key, which would take … <another half minute passes> Just a moment. There’s a man here with a tablet and a clipboard asking for directions. He is from our ventilation contractor. I guess it’s time for an annual inspection. I didn’t know we had that service. The server room is the most-important room to check, he said, so I showed him the way.
All right, yes, where was I? To be completely secure, make sure your password size is up to date. Experts tell us to use phrases instead of words. Utilize the entire alphabet, lower and upper case, special characters and numerals, you know … <someone else arrives> Now there’s a guy here with a badge and a clipboard, saying he’s from the health department because it’s time for our surprise inspection. He has to see every area where the employees eat. He also says he needs to inspect the server room to make sure no one is eating or drinking in there, for safety reasons. Gosh, I didn’t know that was the law. And I didn’t know that health department inspectors wore little tin badges like you see in the toy aisle of the supermarket. Who would have thought?
As I was saying, a 16-letter password is supposed to be orders of magnitude stronger than an eight-letter password, and should resist decryption until well after the sun goes nova … <a minute goes by> That was a guy from the sandwich shop around the corner with a bag of sandwiches, saying he needs to set up lunch in the corner conference room for a meeting. He was a little vague about who lunch was for and especially which conference room it must be in, but I figured it out and led him there, saying it was okay if he wanted to set up his laptop while he was waiting. I hope the health inspector isn’t offended … <phone rings> Wow, it’s busy here today.
The call is from someone from the corporate help desk. He needs the encryption key for our corporate database to reboot the server the database resides on. Who knew?
As I was saying … <phone rings again> Now someone’s on the phone saying he’s from the Microsoft help desk and my computer has a problem. He can show me all these things going on in an applet in the control panel. He had a thick foreign accent, but I understood him when he said there is software I need to download to fix the computer.
I’m sure I’ll get to that. But as I was saying, security software is very important.
Note: These examples of social engineering as a security breach were from a conversation with John Strand, a penetration tester with Black Hills Information Security in South Dakota. Fear him greatly.
For aNewDomain.net, I’m Lamont Wood.
Based in San Antonio, Texas, Lamont Wood is a senior editor at aNewDomain.net. He’s been covering tech trade and mainstream publications for almost three decades now, and he’s a household name in Hong Kong and China. His tech reporting has appeared in innumerable tech journals, including the original BYTE (est. 1975). Email Lamont at Lamont@anewdomain.net or follow him @LAMONTwood.