aNewDomain.net — On Friday President Obama promised more supervision over the NSA. But in the new tech world of the Internet of Things this is almost irrelevant. The President realized that he can not say, “Trust us” anymore. Obama needs to also understand that Silicon valley geeks know that listening is so 20th century…
The truth is we are all heading toward a total surveillance reality. And this new reality will include your home, which is connected to your car, which is connected to your wearable smartwatch and your smart glasses.
Be careful. The Internet of Things (IoT) is becoming more and more personal every day. At some point your toaster and your entire household will become excellent connectors to the PRISM structure. Said ex-CIA chief David Petraeus at an I-Q-Tel forum in March 2102: ” ‘Transformational’ is an overused word, but I do believe it properly applies to these technologies, particularly to their effect on clandestine trade craft.”
In other words, Patraeus is anticipating the day when your toaster will be connected to your Wi-Fi. And when that day arrives, it will enable the NSA to snoop inside your household. The organization will know if you had toast for breakfast and if your life is toast.
Zero Privacy is a term applicable to our wearable future. Everything will be connected in one way or the other.
According to Petraeus, “Items of interest will be located, identified, monitored and remotely controlled through technologies such as radio-frequency identification, sensor networks, tiny embedded servers and energy harvesters — all connected to the next-generation Internet using abundant, low-cost and high-power computing, the latter now going to cloud computing, in many areas greater and greater supercomputing, and, ultimately, heading to quantum computing.” Keep in mind that David Petraeus is the guy who didn’t know how to encrypt his sexy personal Gmail messages.
Petraeus allowed that these household spy devices “change our notions of secrecy” and prompt a rethink of “our notions of identity and secrecy.” All of which is true (and convenient) for an ex-CIA director.
As our lives become more connected to the Internet and to other machines, privacy and security concerns rise as well. The flow of Information is becoming more complex. Who gets this information (personal or otherwise) raises red flags:
- With so much data collection, how are companies using that data? It raises concerns about third-party disclosure, particularly of personal information.
- Check out this previous story about privacy rights for the average citizen.
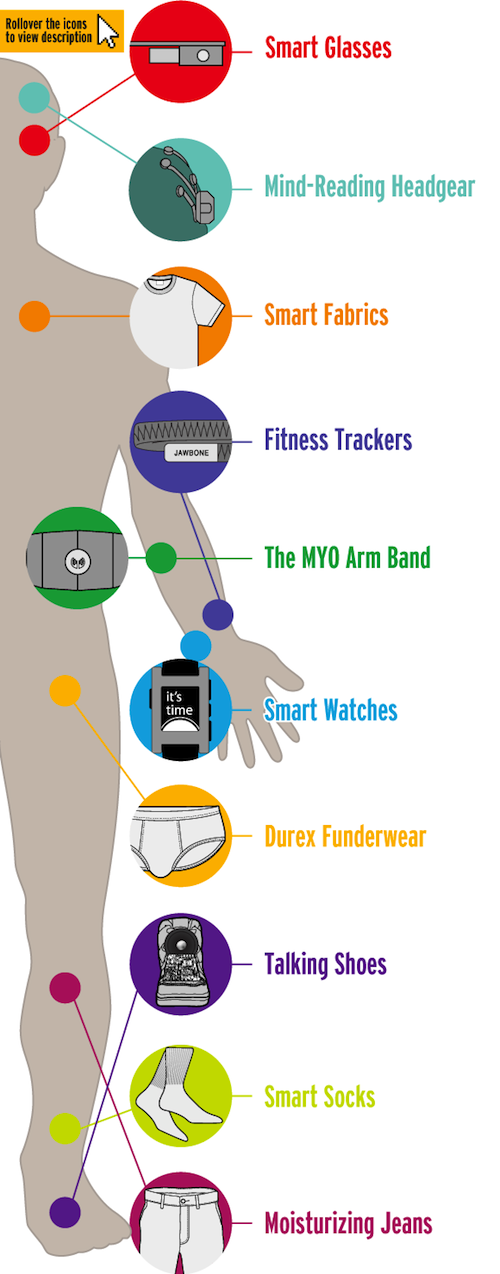
The graphic below profiles a “person of interest.” Introducing the naked wearable citizen:
Image credit: Minyanville
How can there be data minimization when just about everything is collected by a device or a sensor?
- If online tracking is chilling now, the increased-tracking capabilities of IoT will be even-more pervasive. The Electronic Information Privacy Center (EPIC) notes the high degree to which sensitive behavioral patterns can be tracked. As security expert Bruce Schneier has pointed out, businesses will have more “eyes and ears” on consumers. Anonymity will be very difficult in a world where the online and offline world converge. Even network anonymity, as EPIC highlights, will diminish as IPv6 allows more device connectivity and identification.
- Several groups warn of the power imbalance that will be possible between businesses and consumers. One example raises the possibility of loyalty card membership. A store may recognize members, but non-members may not be granted access to the store. The effect could generate geo-fences, social divisions among classes or other demographics. One group even promotes the creation of “privacy habitats” where no connected devices are allowed.
The debate on privacy protection forums — a summary from “future of privacy forum.”
- Data collection versus use. Many argue that collection is inevitable, and that parties should be concerned, not about collection, but about how data is shared with third parties and how businesses demonstrate and exercise accountability and Privacy by Design.
- De-identification is huge. Many argue that it’s okay to collect and share IoT data as long as it’s anonymized. Others note that pure de-identification is just not possible.
- What’s the government’s role in all of this? There seems to be a lot of agreement that policy, if any, should be technology neutral.
- Self-regulation, industry codes of conduct and the FTC’s Section 5 authority will be enough to police the IoT world. ICANN points out there are several self-regulatory initiatives already underway.
- How can individuals have control in an über-complicated IoT world? Applying the FIPPs to IoT may be challenging.
- Who owns the data? Several groups point out the importance of clarifying a data-ownership framework.
Go here for more information concerning NSA data mining and the PRISM program.
If you want to read an Optimistic view of IOT go to my friend Maya from SF view.
Based in Australia, David Michaelis is a world-renowned international journalist and founder of Link Tv. At aNewDomain.net, he covers the global beat, focusing on politics and other international topics of note for our readers in a variety of forums. Email him at DavidMc@aNewDomain.net.














Good stuff!
-RAP, II
I am being turned into a Luddite by my government! I don’t want any of this stuff!
Thanks David. Definitely a sickening reality.
[…] senators will have to understand the new tech realities as I’ve pointed out to aNewDomain.net readers just this […]
[…] https://anewdomain.net2013/08/05/iot-well-spy-on-you-through-your-toaster-and-wearables-prism-and-pe… […]